Manage certificates for your Bosch IoT Hub tenant
Bosch IoT Hub allows your devices to authenticate based on X.509 client certificates.
However, for any device certificate to be recognized, the root certificates (aka CA certificates) with which the device certificates were signed need to be uploaded to your Bosch IoT Hub tenant.
In order to continuously provide a valid certificate for your devices, you have two options:
Add a certificate
Before it expires you can either
Add a new certificate
In this case you have a time frame where both certificates would be valid, and you can delete later the expired certificate.
orReplace a certificate with a new one.
We support you in managing up to 5 certificates per tenant.
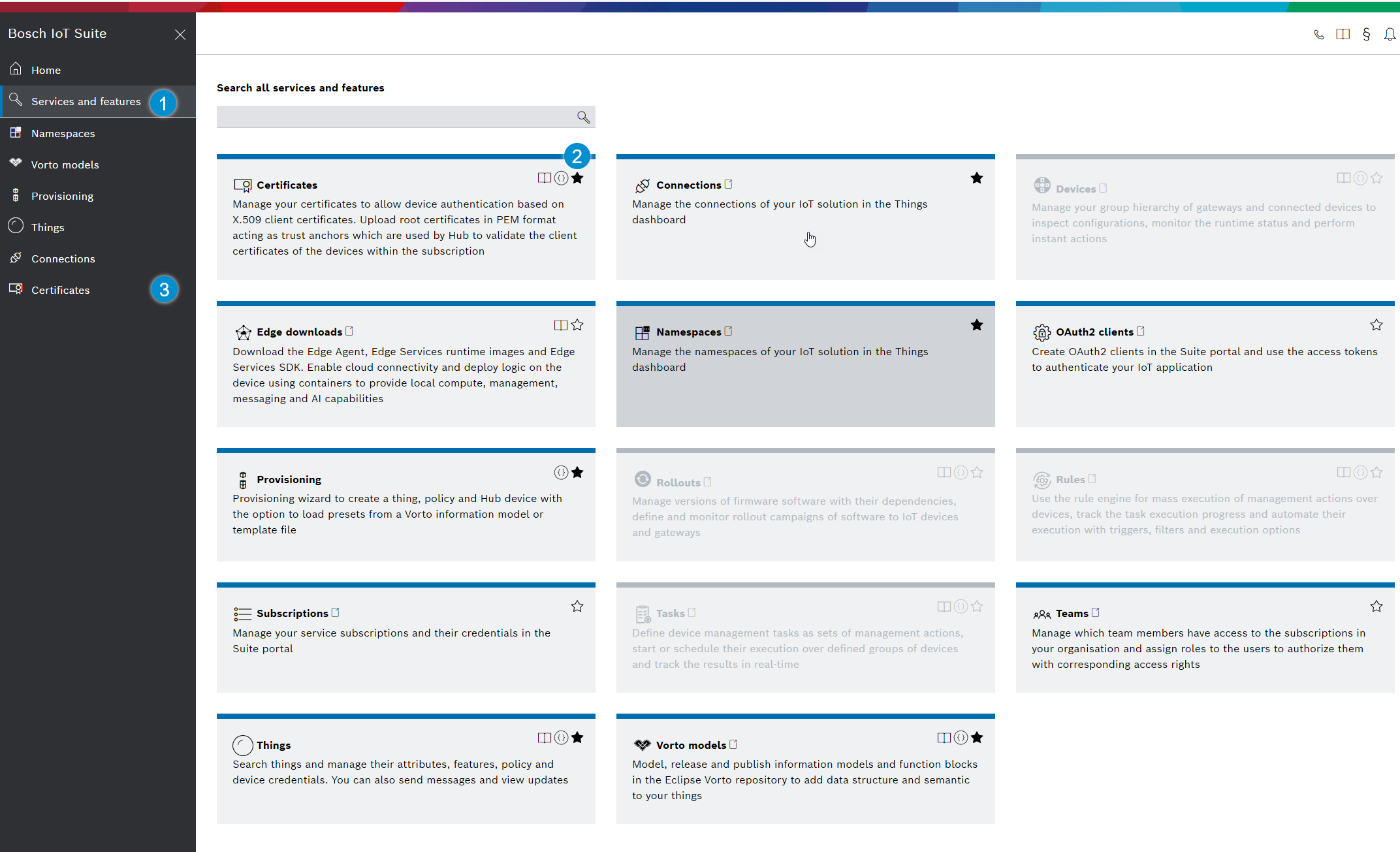
This can be achieved either via Bosch IoT Hub - Management API or by using the Bosch IoT Suite Console.
This example shows how to proceed using the Bosch IoT Suite Console.
Add a certificate
In case someone has already uploaded root certificates, these are listed in the Root certificates view.
In this view, you can add up to 5 root certificates in PEM format for the current subscription (aka Hub tenant).
The order of the listed root certificates is not relevant.
Alternative A - load PEM file
Click the Load PEM file button.
Select it from the local folder where you store it
Confirm with Open to upload it from your workstation.
The entry field is pre-filled with the Base64 encoded certificate.
Click Add to save it.
Alternative B - copy the Base64 encoded certificate into the entry field
Use the Root certificate (PEM format) entry field. E.g.
-----BEGIN CERTIFICATE-----MIID7zCCAtegAwIBAgIJAMgK95c7xFAIMA0GCS...BAoMBUJvc2NoMRAwDgYDVQQLDAdJT0MvUEFQMR...-----END CERTIFICATE-----Click Add to save it.
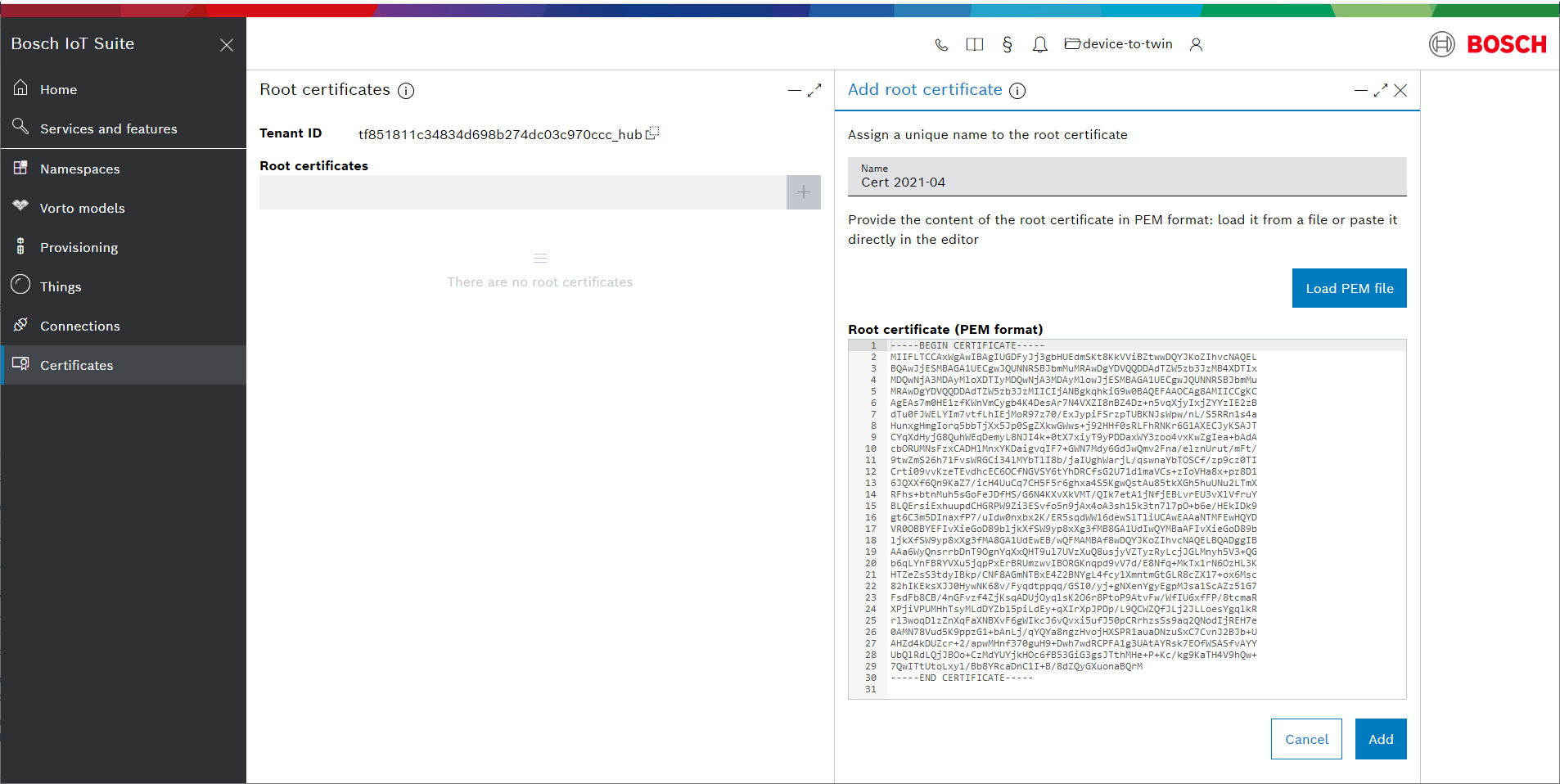
X.509 certificates act as trust anchors (e.g. with different validity periods). They can be self-signed or can be issued by a certificate authority (CA) and are used to sign the client certificates of the devices.
Client and root certificates, also referred to as CA certificates, are processed by Bosch IoT Hub to verify the identity of all devices belonging to a related subscription (aka Hub tenant).
Use the "add" operation for following cases:
It is the first certificate for this tenant.
You want to upload a certificate with validity period in future and you want that the current valid certificate stays unchanged.
Replace a certificate
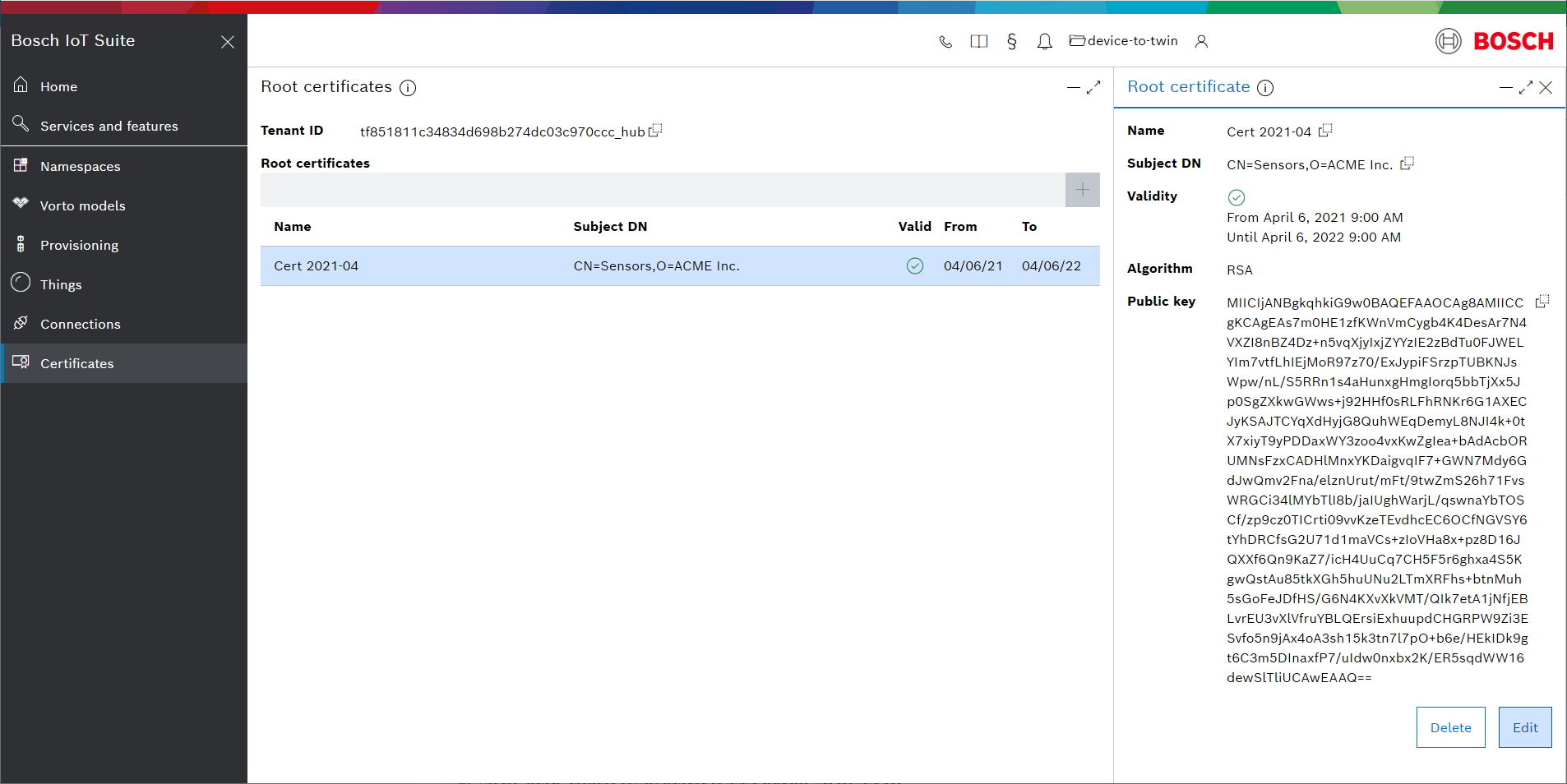
In the Bosch IoT Suite UI, navigate to the certificate you want to replace.
Click the certificate from the first table.
As you can see, the certificate in our example is valid until 2022. It will be replaced with a new one, which is valid until 2023.
In the new section at the right side click Edit.
Check the Replace content checkbox and upload the new certificate.
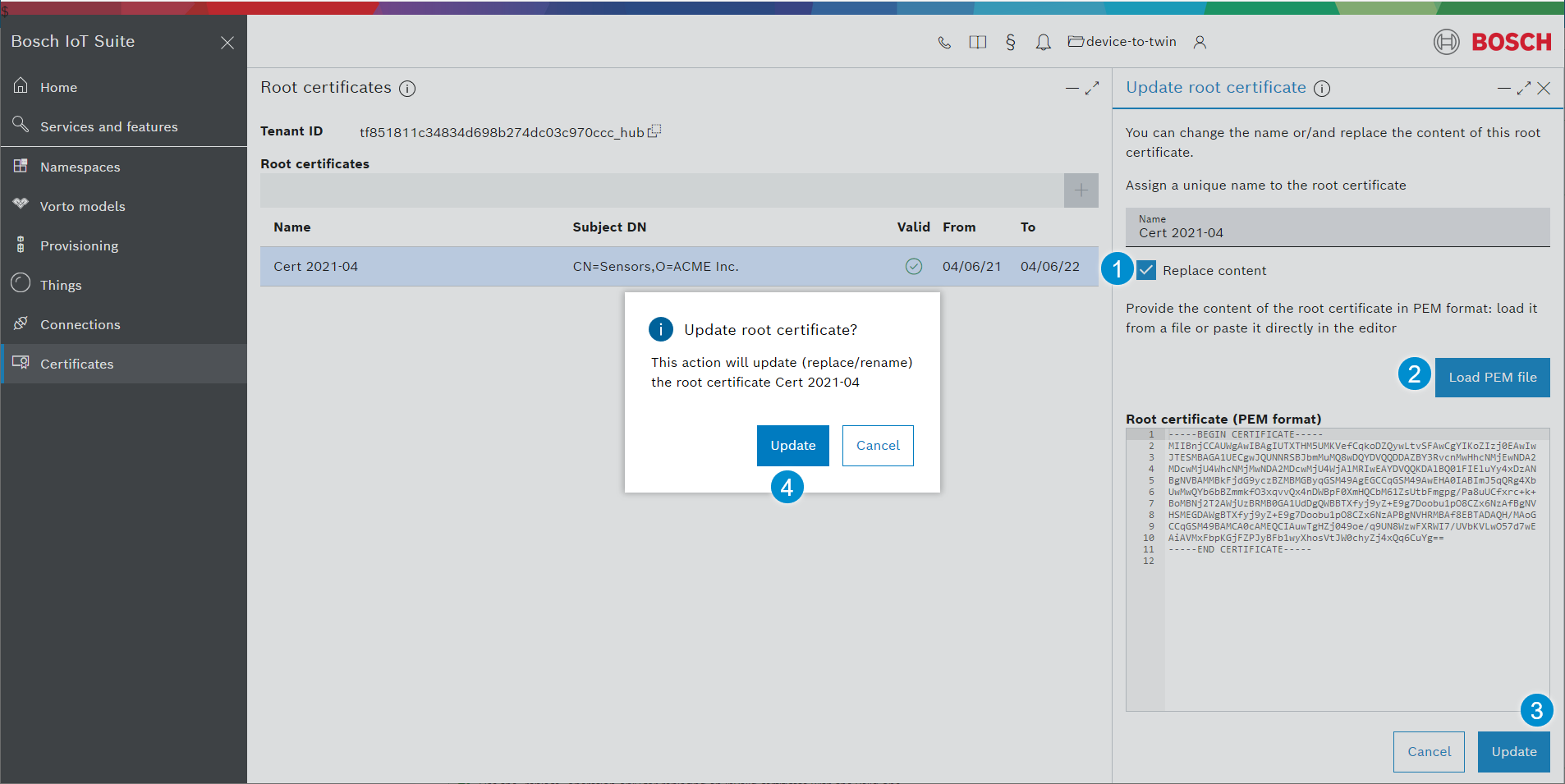
Finally, confirm with Update.
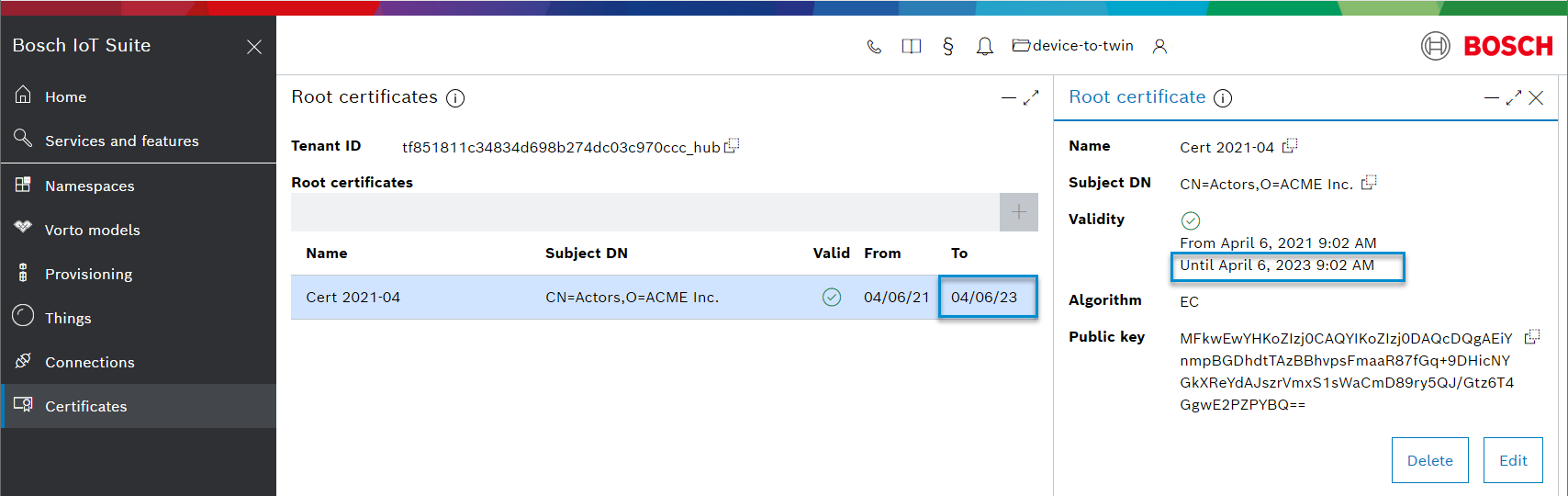
As you can see, the new certificate in our example is valid until 2023
Use the "replace" operation only for replacing an invalid certificate with the valid one.
If you want two certificates to be valid in parallel, use "add" instead.
Read notifications about an expired certificate
As soon as the validity period of a certificate expires, users working with the Bosch IoT Suite UI will be notified respectively.
Example:
The red marker for notifications is visible, even if you work in another view.
In the Root certificates view, the certificates mentioned in the notifications are marked respectively.
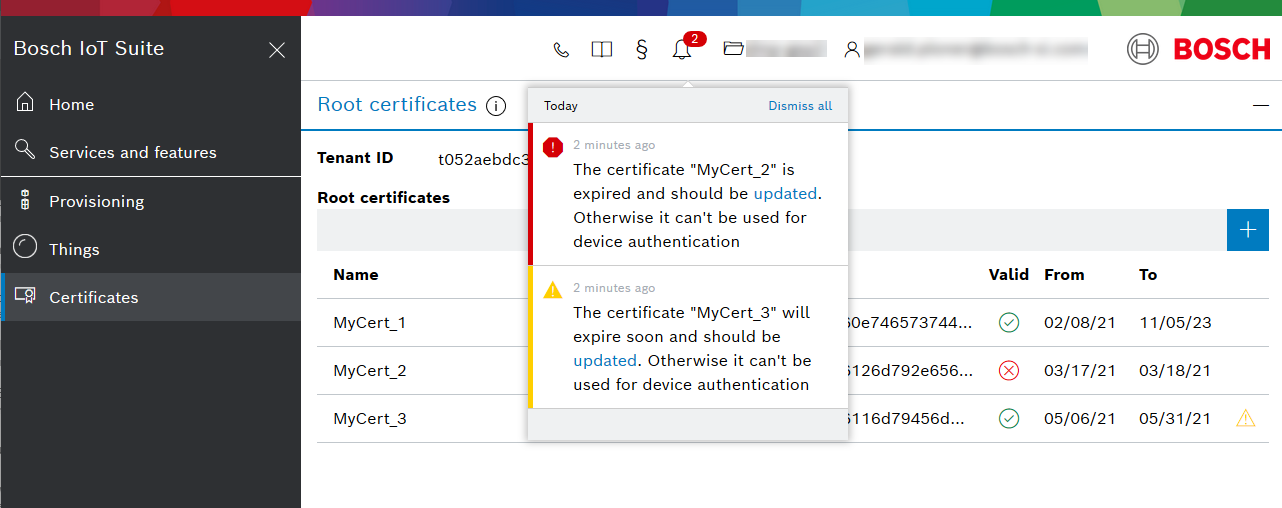
The warning notification is issued 30 days before the certificate expires, thus your team has plenty of time to replace it.